A Cyber and Data Breach Insurance solution that is easy to implement, understand and utilize if needed.
Our market leader insurance carrier partner combined with our superior claims and breach response services help you cover the financial costs associated with a cyber or data breach – and allows you to get back to business with little interruption or reputational damage.
The role of Cyber and Data Breach Insurance
Insurance can't eliminate a data breach or be a replacement for data security, but it can provide a backstop of financial relief. Cyber insurance helps tame the significant costs of a cyber attack and/or data breach by offering coverage to help cover your costs. These costs can be extensive as you have to respond to, as well as minimize the damage of a data breach or cyber attack. The insurance can help to pay for the data breach notification and credit monitoring, forensics and investigations, business interruption, data recovery and repair, regulatory fines and penalties, and potential extortion threats.
Play VideoWHAT DATA IS AT RISK?
In simple terms, any data maintained by your business is valuable to someone. Whether it's stealing employee social security numbers to fraudulently establish new lines of credit or extracting other confidential information to sell on the black market, access to personal and confidential information can be easily monetized. Other types of data about your clients, or company trade secrets may be of value to competitors or cyber terrorist.
To protect individuals' personal information, strict requirements have been placed on businesses to pay the costs associated with responding to a data breach. The overwhelming costs and confusing legislative requirements make it difficult for businesses to overcome the fallout of a data breach without assistance.
KEY FACTS
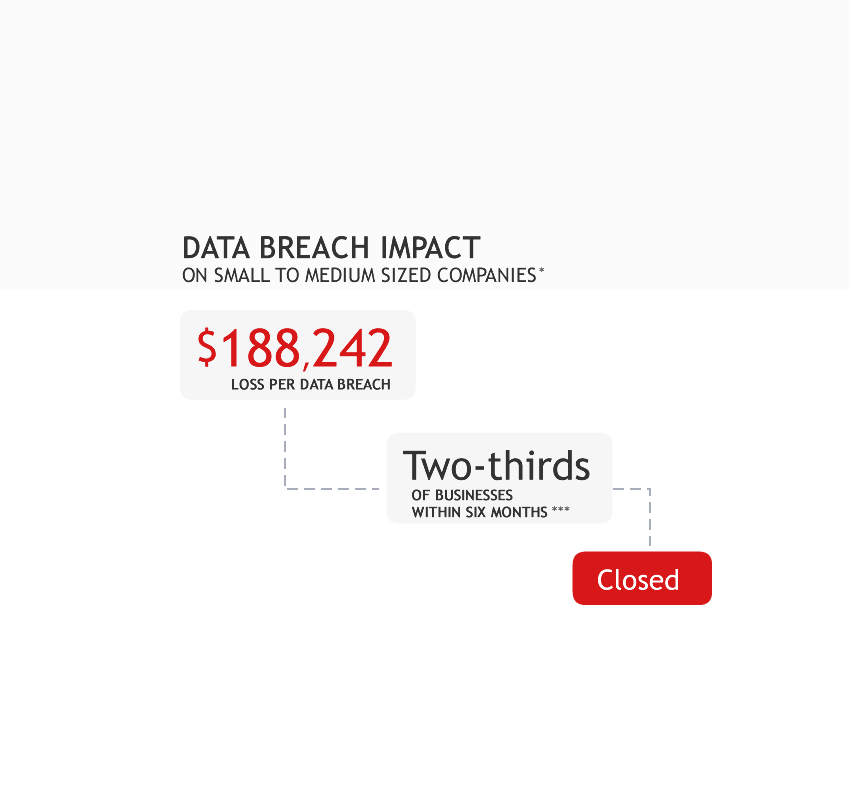
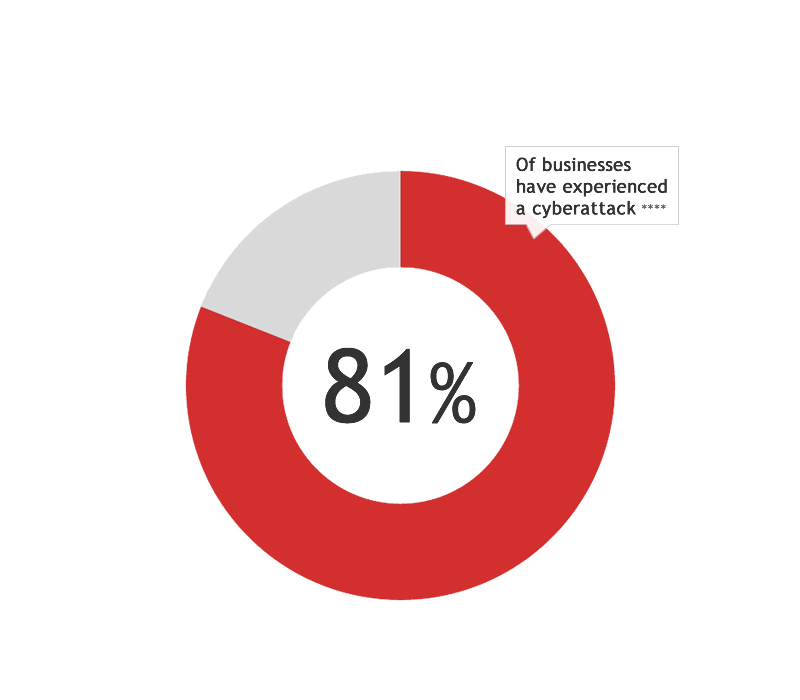
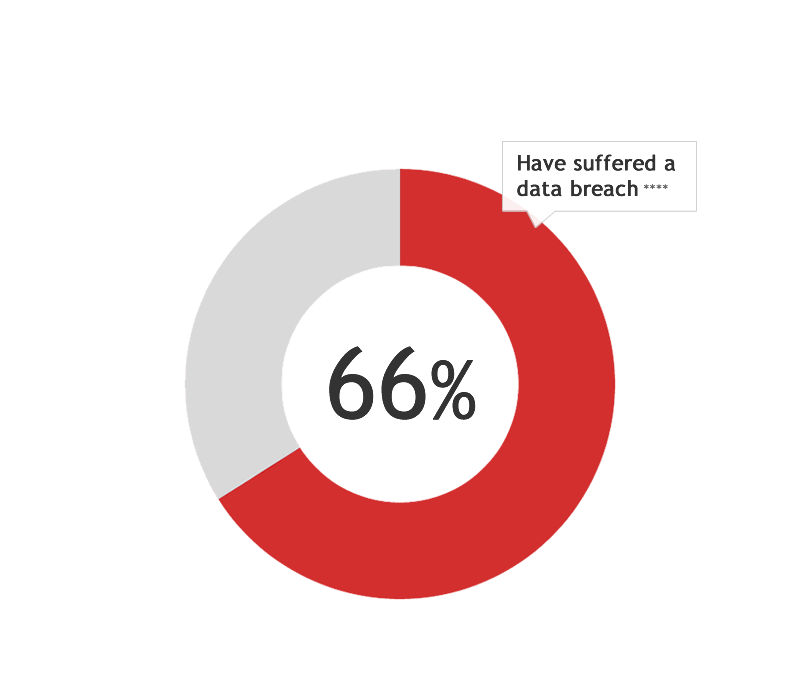
Malicious actors continually seek new security vulnerabilities to exploit and access valuable and sensitive information. Many companies believe privacy and data breaches won't happen to them, but three key facts stand:
Fact 1:
Breaches are bigger and more costly than ever before
Fact 2:
Every industry and size of business is at risk
Fact 3:
All organizations are susceptible to both internal and external threats
INSURANCE COVERAGE OPTIONS
What coverage is needed to insure the many exposures facing businesses today?
Standard Coverage:
While there is no 'one size fits all' approach to adequately insure all privacy exposures, we do offer a comprehensive insurance package that provides coverage
to meet the needs of most businesses. The standard package includes coverage for the following:
Covers costs to defend and resolve claims with regard to the handling of personally identifiable or confidential corporate information. Covers negligence, violation of privacy or consumer protection law, breach of contract and regulatory investigations. Covers issues resulting from the failure of network security, including the negligent transmission of a virus and the inadvertent participation in a DDoS attack against a third party.
Coverage for costs associated with responding to a breach, such as forensic costs to confirm and identify the breach, costs to notify affected individuals, credit protection services including costs to staff a call center for redemption of monitoring offers, and crisis management and public relations costs.
Covers financial loss, such as business income when a company has its network-dependent revenue interrupted. Traditionally, this has been for fire, flood, etc. but technology growth has created new BI perils (viruses, tech failures, programming errors and computer hacking).
Covers costs to recreate or repair damaged or destroyed data, systems or programs. In a digital world, property is no longer exclusively tangible, so specialized coverage is needed to pay for intangible data recovery costs.
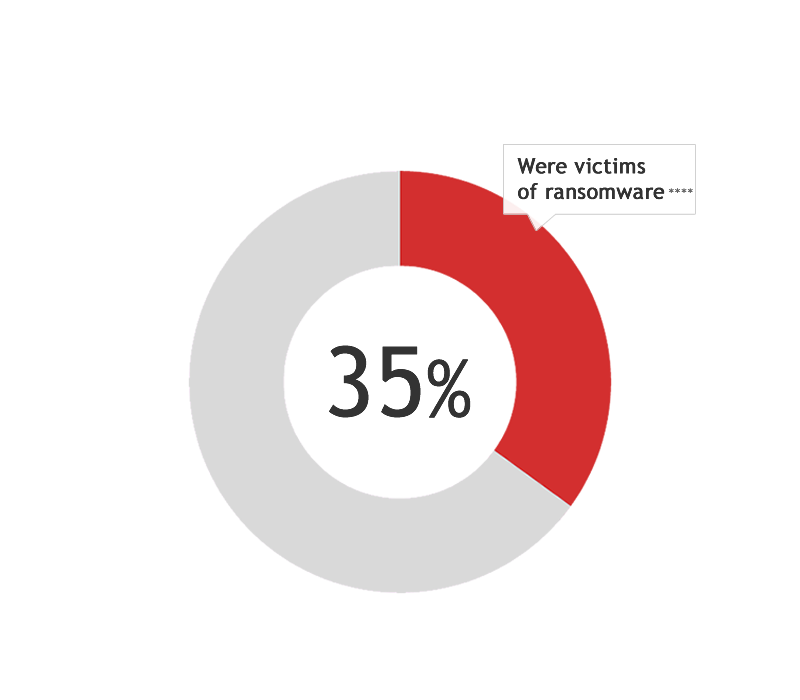
Covers the response costs and financial payments associated with network-based ransom demands. With the proliferation of ransomware such as Cryptolocker and anonymous currencies such as Bitcoin, network extortion demands are on the rise. In the digital world, intangible assets are 'kidnapped' and extorted with threats to shut down a system or divulge sensitive or proprietary information.
Coverage for acts of terrorism is included in your policy, as amended in 2015, by the TRIA (Terrorism Risk Insurance Act).
if your company processes credit / debit card transactions this coverage will be automatically included.
Optional Coverage Enhancements:
Companies must each assess their own exposures and purchase coverage that specifically caters to the risks inherent to their specific business.
As such, addition optional coverage enhancements made be added for the following:
Costs to defend and resolve claims related to online content, such as defamation or trademark or copyright infringement.
This additional endorsement to provide coverage (subject to the selected sublimit) for losses incurred when some criminal disguises as a vendor, client or employee and tricks the insured’s employee into transferring funds to an account not under the control of the company.
FREQUENTLY ASKED QUESTIONS
There can be a lot of confusion around Cyber and Data Breach Insurance. We are here to help answer some of the most common questions you may have regarding privacy exposures and coverage.
Why purchase Cyber Insurance from Cyber Insurance
Simple and Affordable
Comprehensive Coverage
We are Specialists
Loss Prevention Services
Client Portal
Rapid Breach Response
Fast Claim Processing
Access to Experts
Membership in the CDSA
* Source - Verizon Communications Data Breach Investigation Report
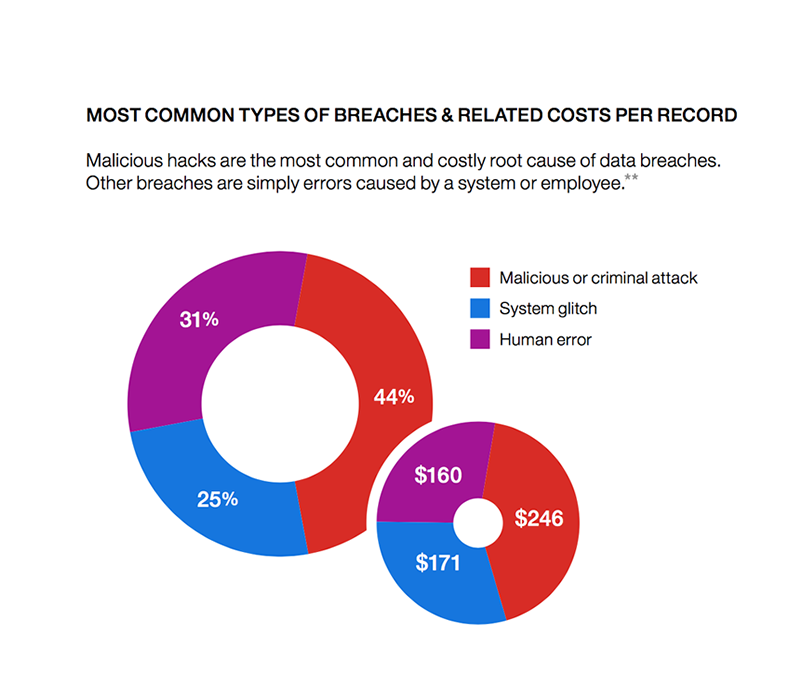
** Source - Ponemon Institute® LLC and IBM®
*** Source - National Cyber Security Alliance
**** Source - Osterman Research 2017 SME Cyber Security Survey